By: Karl Rubin, COO
Lessening the impact of security vulnerabilities in software applications is becoming an essential priority for organizations. Slow response time, complexity of new tools and technologies, and the rise of an ever smarter adversary creates a challenging climate for IT providers and cybersecurity experts.
What is Application Security?
Application Security is like injecting an immunity booster inside an application right from the start of the development stage. It is an approach where security features are developed, augmented, and added within applications. This helps to prevent attacks, breaches, and to minimize vulnerabilities in that application. Finding, fixing, and proactively strengthening application security of software is imperative. But is it easy?
Today, applications have become prone to attacks, leaks, exploits, and new velocity and variety risks. No wonder mobile application security sits right at the top of many businesses’ risk list. According to the annual Cost of a Data Breach Report 2021 by Ponemon Institute, the average cost of a data breach is about $4.24 M, and there is a 10 percent rise in the reported average cost in 2020-21. Also, it takes about 287 days to identify and contain a breach. With more and more employees accessing data through their devices, workforce and data becoming more and more distributed, and with new lean approaches being embraced during application development – the scenario is getting murkier and scarier than ever before.
Core Issues in Application and Software Security
While approaches like DevOps and agile methodologies have made applications lightweight, fast, and robust, many issues lurk in the shadows.
According to the Global CIO 2020 Report, 11 percent is the average proportion of all application and infrastructure environments that digital teams fully observe. And 90 percent of organizations hint at barriers that prevent them from monitoring a more significant proportion of their applications.
Many enterprises struggle with roadblocks in monitoring applications. Monitoring tools in place don’t offer the fast ‘time to value’ or ease of use to make it worthwhile. There is almost no capacity to triage and analyze additional monitoring data (26 percent), and it takes too much time to instrument monitoring capabilities (34 percent). Also, for 38 percent of CIOs, the huge problem that emerged is that the number of different solutions needed makes it difficult to operate efficiently.
How can you make sure that applications run smoothly and safely when 32 percent of organizations say their IT environment changes at least once per second, 61 percent of organizations say their IT environment changes every minute or less? How to stay abreast of new attacks and risks when 74 percent of CIOs say their organization will lose their competitive edge if IT cannot spend less time “keeping the lights on”?
Not just that – there are many other problems that organizations have to confront in the present application landscape.
There are weak server-side controls, which wreak havoc when any communication between an application and the user outside the mobile device goes through a server – such servers become sitting ducks for cybercriminals. Enterprises also fight with inadequate security budgets and a lack of cybersecurity knowledge. There is a preponderance of mobile OS for security updates and responsibility. Plus, many vulnerabilities exist due to cross-platform development and compilation. Many server-side components contain vulnerabilities that can disrupt app operation.
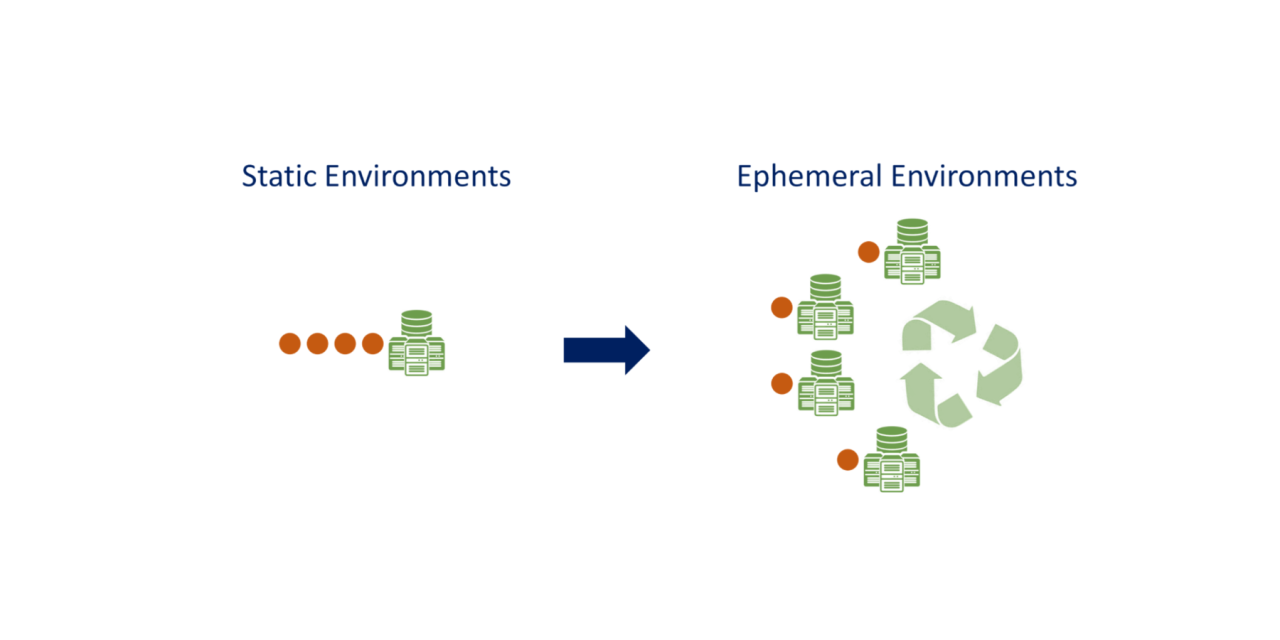
Then, there is the sheer scale and complexity of the cloud to deal with. Gartner has predicted that the end-user organization will cause 99 percent of cloud security failures by 2025. It has been noted that cloud-native architectures could be fundamentally breaking application security. Here, traditional approaches to vulnerability management make it challenging for enterprises to stay up to date with dynamic environments. The habits and tools for a static view do not cut here. This leads to many blind spots being easily skipped. Most vulnerability scans happen in the pre-production stage, so they miss production-stage red flags. The confusion thrown around due to the volume of false positives is another factor to navigate.
Also, enterprises have not entirely solved issues that are arising because of unsafe data storage, as the standard practice for developers is to depend upon the client for data storage. This is rarely a sandbox environment and is a ripe spot for data breaches.
It is easy for such applications to be easily exploited and manipulated. The problem is worsened because of practices of easy authorization and authentication.
Understanding, Prioritizing and Managing AppSec Vulnerabilities
Interestingly, the rise of agile practices and DevOps and the adoption of continuous delivery processes are also turning into challenges in a new way. Here, new features or updates get launched within days or even minutes. That means that traditional security solutions can lack compatibility, and the emergence of complex production environments raises the risks in a manifold way.
Organizations are running multiple parallel versions in production with staggered rollouts, A/B testing, Beta testing, and blue-green deployments. That means there is a high likelihood of chance vulnerabilities that are skipped by time-consuming manual scans. Inaccuracy and misconfiguration make the scenario riskier.
Add to that: the constant pressure to “shift left.” When developers have an extra responsibility to ensure that code does not expose any vulnerabilities before it goes live, developers may not have the capacity, time, or expertise to analyze, assess, and manage vulnerabilities that pop up in scan results. It is difficult to manually manage and scan dynamic, cloud-native applications for vulnerabilities.
Look at what IDC predicts. By 2022, 90 percent of new enterprise applications will be cloud-native, using agile methodologies, and API-driven architectures. With modern development practices, the burden for identifying application security vulnerabilities is shifting to developers and DevSecOps teams. Can they manage it, though? 61 percent of organizations, say their environment changes once every minute or less, and for nearly a third, it changes at least once per second?
A Single Source of Truth
We need a single source of truth for application vulnerabilities so teams get real-time insights that allow them to focus on production-relevant exposures and help fix high-priority vulnerabilities first and build DevSecOps processes that can secure continuous delivery. This can be supported with automation, AI, and agility in application monitoring and testing.
Enterprises need to expand the coverage of applications, especially in production. This will help them find blind spots, detect vulnerabilities in real-time, and gain information to assess risks. There is an excellent need for visibility across the entire cloud and IT environment. There is a need for automation to reduce manual instrumentation and intervention. Teams should gather ease of use and rapid time to value from performance management solutions. Plus, they should bolster their ability to correlate alerts and reduce noise so IT teams can focus on what matters to the business. It would help immensely if they can capture metrics, logs, and traces in a single platform.
Final Thoughts
Gartner predicts, through 2025, 90 percent of the organizations that cannot control public cloud use will inappropriately share sensitive data. Also, by 2024, most enterprises will continue to struggle with appropriately measuring cloud security risks. Now, add to that the possibility that through 2025, 99 percent of cloud security failures will be the customer’s fault.
Yes, the cloud and the adjacent complexity of these new technologies will add more barriers to the success of application security. CIOs need to enforce policies on cloud ownership, responsibility, and risk acceptance. A life cycle approach to cloud governance is highly recommended, along with central management and monitoring plans to cover the inherent complexity of multi-cloud use.
The emphasis on applications security needs to go deeper and stronger as we see digital transformation gaining more and more pace. According to the 2020 CIO Global report, 89 percent of CIOs say their digital transformation has sped up in the last 12 months, and 58 percent say their digital transformation will continue to speed up. There is increased pressure on IT teams for increased demand for IT services (64 percent) and because IT is becoming more of a business imperative (56 percent). Also, 56 percent of CIOs say they almost never complete all the tasks the business needs from IT because of the time and resources drained by “keeping the lights on.”
Microservices, containers, and Kubernetes are helping organizations achieve the agility they need to speed up innovation, but the complexity of managing these ecosystems is increasing.
This adds new challenges for the already stretched cloud and IT operations teams struggling to keep up. 63 percent of CIOs say the complexity of their cloud environment has surpassed human ability to manage.
When containers and microservices come and go in seconds, IT teams face a volume, velocity, and variety of data from metrics, logs, and traces. So, it’s time to reflect on the relevance of manual approaches to configure and instrument apps or script and source data. We need fresh approaches and capabilities to manage this scale, complexity, and frequency of change.
Application Security will need a significant shift – in tools, mindset, and automation. It won’t be full-proof, but it will be future-proof.